FirstWare DynamicGroup 2018
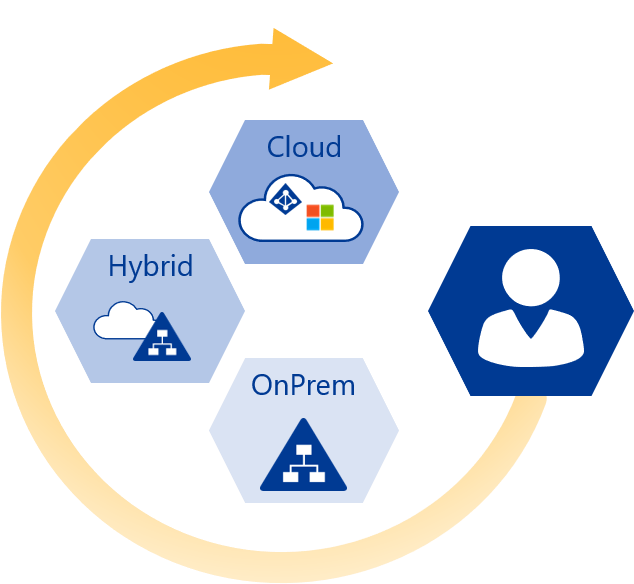
FirstWare DynamicGroup 2018 creates dynamic groups by itself. The new 2018version of FirstWare DynamicGroup is now available and offers manyinnovative and time-saving features.
Essentially, it is a powerful tool to automate groupmemberships of AD objects. It accelerates processes andreduces the workload for IT-departments.The software application isused across a variety of industries in countries situated allaround the globe.
Smart Creation: Upload 100 groups in 10 seconds
Self-creating groups and mass editing transform DynamicGroup2018 into a versatile tool to manage AD groups.
Get a flying start with DynamicGroup Wizards
Clever creation of groups based on attributes andOUs
The new “Smart Creation Wizard” automatically createsdynamic groups with the help of clever filter options.Depending on the selection, users, groups, computers and/orcontacts are saved in new dynamic groups, based on a pre-definedattribute or OUs.
Just select the appropriate settings by using the wizard andstart the process. DynamicGroup confirms the successful creation ofall the new groups with a status message.
Create multiple dynamic groups with bulkimport
Whoever wants to create multiple dynamic groups atonce is going to like the new “Bulk Import Wizard”.Hundreds of groups can now be uploaded to the DynamicGroup consoleby using csv files which contain all theattributes that are required. This new feature saves precious timeespecially for mass imports as there is no needfor manual entry of data.
Copy dynamic groups as templates
The DynamicGroup Console offers another very useful new feature,the option to copy groups. It means that an existing dynamic group can be used as a template for a new group.It basically simplifies and accelerates the creation of newgroups.
There are two easy ways to copy, either by using the “Copy” iconor by clicking on the right mouse button and selecting”Copy Group“. After entering the group name, groupscope and group type DynamicGroup creates a copy of the group withthe most important dynamic attributes.
Focus on users and easier handling of group administration
All the improvements in DynamicGroup 2018 focus on userfriendliness and simplified AD group administration.
Identify groups fast with the help of prefixes
It is recommended to add a prefix to the groupname when creating a new group. It helps to identify thegroup at once. For example, dynamic groups can be recognised easilyif they have the prefix “DG-” in their group name.
The configuration tab in DynamicGroup 2018 now includes theoption to set up prefixes in advance. Once a new group is beingcreated these prefixes appear in a dropdown menu from which aselection can be made. Hence, the goup name will start with theselected prefix.
Delete multiple groups at once
In the group overview, multiple groups can be marked and deletedat once. Proceed by simply clicking on the right mouse button andselecting “Delete Group”.
Automatic special character replacement
Attribute values may contain special characters (e.g. &, |,<, >, %) which are used as filter symbols. Up until now thesehad to be changed manually in the LDAP query. When using the QueryBuilder to create a new LDAP query for a group, the criticalcharacters will automatically be replaced by the correspondinghexadecimal ASCII code. In other words, special characters can nowbe used for queries. Using the Query Builder remains easy anderrors in writing LDAP queries are avoided.
Further changes
Windows Server 2016 compatibility
With the new server version from Microsoft, extended firewall rules were made standard that prevented Dynamic Group from installing the service remotely. This issue has been resolved andthe service can be installed and used normally in Windows Server2016 environments.
System requirements
Until now it was possible to install DynamicGroup on any clientor server in your domain. In this release however, the DynamicGroupConsole will not start any longer if it is installed on a domaincontroller. This is to prevent certain security issues, sinceDynamicGroup would require elevated rights for many operations on adomain controller.
Bugfixes
FirstWare DynamicGroup 2018 includes a number of bugfixes fromthe previous version.
About DynamicGroup 2018
DynamicGroup is a proven product which has been used for manyyears now by a steadily growing customer base.
FirstWare DynamicGroup is a software application to automate groupmemberships in Active Directory. Group members are dynamically assigned to a group based on AD attributes (like department), OUs,combined LDAP filters and more.
30 days trial and further information